As a DevOps engineer, I've watched countless e-commerce teams scramble to fix unauthorized price changes that cost thousands in revenue within minutes. What starts as a simple content management system vulnerability can quickly spiral into customer trust issues, competitor intelligence theft, and devastating profit margins.
With global online retail projected to reach $6.88 trillion by 2026, the attack surface for content manipulation has never been larger. In my experience, the teams that survive and thrive are those who implement robust website content change detection before they need it, not after their first incident.
The Growing Threat of Unauthorized E-commerce Content Changes
Price Manipulation Attacks on the Rise
The sophistication of attacks targeting e-commerce content has evolved dramatically. I've seen teams discover pricing changes hours after they occurred, resulting in products sold at 90% discounts or competitors gaining access to proprietary pricing strategies.
Modern attackers don't just target obvious vulnerabilities. They exploit content management workflows, API endpoints, and even third-party integrations to modify prices, descriptions, and availability data. The rise of automated trading bots and AI-driven purchasing systems means these changes can be exploited at scale within minutes.
Impact on Revenue and Customer Trust
Time to change has become the critical benchmark in 2026. Every hour added to detection and response is margin lost, especially during high-traffic periods or promotional campaigns.
I've worked with teams who lost $50,000 in a single afternoon because unauthorized pricing changes went undetected during a flash sale. Beyond immediate revenue impact, customers who encounter inconsistent pricing or manipulated product information lose trust in the brand.
Customer retention metrics like repeat purchase rate and time to second purchase suffer significantly when content integrity issues create confusion or perceived deception. In North America and EMEA markets, post-purchase experience quality directly impacts weekly retention rates.
AI-Driven Shopping Amplifies Risks
The emergence of agentic AI that autonomously makes purchasing decisions has fundamentally changed the stakes. AI agents infer product information from dynamic content, making data integrity absolutely critical for marketplace visibility.
Unstructured or inconsistent product data now leads to lost visibility in AI-powered search engines and marketplaces. I've seen e-commerce sites lose 40% of their organic traffic when AI systems couldn't reliably parse their product information due to frequent unauthorized changes.
Clean, LLM-ready data with standardized attributes has become essential. Marketplaces increasingly penalize sites with stale or manipulated pricing, as AI systems flag inconsistencies that suggest poor operational reliability.
Understanding Website Content Change Detection for E-commerce
Website content change detection is the practice of continuously monitoring specific elements on e-commerce sites to identify unauthorized or unexpected modifications in real-time.
What Content Changes to Monitor
The most critical elements to monitor include product prices, inventory levels, product descriptions, promotional banners, shipping costs, and payment options. I typically recommend starting with pricing and availability, as these have the most immediate revenue impact.
Beyond obvious targets, monitor category pages, search result rankings, and checkout flow elements. Attackers often modify shipping costs or payment processing fees to siphon revenue without triggering obvious price alerts.
Don't overlook metadata and structured data markup. Changes to schema.org product markup can impact search engine visibility and AI agent interpretation, leading to longer-term traffic losses.
Real-Time vs Scheduled Detection
Real-time monitoring prevents immediate revenue impact but requires more infrastructure investment. I've implemented systems that check critical pricing elements every 30 seconds during peak hours and every 5 minutes during off-peak periods.
Scheduled detection works for less critical content like product descriptions or promotional banners. However, for pricing and inventory data, even a 15-minute delay can result in significant losses during high-traffic periods.
The optimal approach combines both: real-time monitoring for revenue-critical elements and scheduled scans for comprehensive content auditing. This balance provides protection without overwhelming your monitoring infrastructure.
Visual vs Text-Based Monitoring
Text-based monitoring examines raw HTML, API responses, and database values to detect changes in the underlying data. This catches modifications before they reach customers but may miss display issues caused by CSS or JavaScript problems.
Visual monitoring captures how changes appear to actual users, identifying display tampering that could confuse customers even when underlying data remains correct. I've seen cases where CSS injection caused prices to display incorrectly while backend data stayed unchanged.
The most effective approach uses both methods in a layered strategy. Text monitoring provides rapid detection of data changes, while visual monitoring ensures the customer experience remains intact.
Common E-commerce Content Change Vulnerabilities
Unauthorized Price Modifications
Pricing system vulnerabilities often stem from inadequate access controls on content management systems or APIs. I've investigated incidents where former employees retained CMS access months after termination, leading to malicious pricing changes.
Third-party integrations represent another common attack vector. Inventory management systems, pricing tools, and marketing automation platforms often have write access to product data without proper audit trails.
Database injection attacks targeting product tables can modify pricing at scale. Weak input validation on admin interfaces allows attackers to bulk-update prices across entire product categories.
Product Description Tampering
SEO poisoning through description changes has become increasingly sophisticated. Attackers inject keywords, competitor mentions, or malicious links into product descriptions to manipulate search rankings or redirect traffic.
I've seen cases where subtle description changes were designed to trigger compliance violations with payment processors or advertising platforms, forcing temporary business disruptions.
Automated content generation tools can also introduce unauthorized changes when AI models are compromised or configured incorrectly, leading to inappropriate or inaccurate product information.
Competitor Scraping and Data Theft
Aggressive price scraping attempts often leave traces in access logs and can trigger content change alerts when scrapers attempt to verify pricing accuracy through form submissions or API calls.
Sophisticated competitors use distributed scraping networks that gradually harvest pricing intelligence while attempting to blend in with normal traffic patterns. Content change detection can identify unusual access patterns to pricing-sensitive pages.
Some scraping operations attempt to modify competitor pricing through automated attacks, hoping to trigger pricing wars or gather intelligence about automated repricing systems.
Supply Chain Disruption Impacts
Global supply chain volatility requires rapid content updates when products become unavailable or pricing changes due to tariffs and shipping costs. Delayed updates can result in overselling unavailable inventory or maintaining outdated pricing.
I've worked with teams managing thousands of SKUs where manual content updates couldn't keep pace with supply chain changes, leading to customer service issues and refund requests.
Automated supply chain integrations can introduce unauthorized changes when external systems are compromised or misconfigured, making content change detection essential for maintaining data integrity.
Implementing Content Change Detection: Technical Approach
Setting Up Monitoring Rules
Start by identifying your most revenue-critical elements using a simple risk matrix: impact versus frequency of change. Product prices, availability status, and checkout flow elements typically rank highest.
Define monitoring thresholds that account for legitimate business processes. For example, allow scheduled price updates during maintenance windows but alert on any pricing changes outside approved timeframes.
Here's a basic monitoring configuration approach:
- Critical Elements (Real-time): Product prices, inventory status, checkout totals
- Important Elements (5-minute intervals): Product descriptions, shipping costs, promotional banners
- Standard Elements (Hourly): Category descriptions, footer content, policy pages
Create element-specific rules that understand normal variation patterns. Price monitoring should account for currency fluctuations and promotional schedules, while inventory monitoring should expect regular updates from fulfillment systems.
Alert Configuration Best Practices
Configure immediate alerts for pricing changes exceeding predefined thresholds. I typically set alerts for any price change greater than 10% or any change occurring outside approved maintenance windows.
Implement escalation procedures that notify different teams based on change severity and type. Pricing changes require immediate attention from revenue operations, while description changes might only need content team notification.
Use smart grouping to prevent alert fatigue during legitimate bulk updates. If your inventory system updates 500 products simultaneously, group these into a single notification rather than flooding operations teams with individual alerts.
Consider implementing automatic rollback triggers for critical changes. When unauthorized price modifications are detected, automated systems can restore previous values while human teams investigate the root cause.
Integration with DevOps Workflows
Integrate content change detection with your existing incident response systems. Tools like PagerDuty, Opsgenie, or ServiceNow should receive structured alerts that include change details, affected elements, and suggested response actions.
Connect monitoring systems to your CI/CD pipeline to distinguish between authorized deployment-related changes and unauthorized modifications. This prevents false positives during legitimate content updates.
Implement audit trails that track all content changes, including user attribution, timestamps, and change details. This forensic capability proves essential during security investigations and compliance audits.
Consider integrating with content monitoring platforms that provide comprehensive change detection across multiple site elements, offering both real-time alerts and historical change analysis.
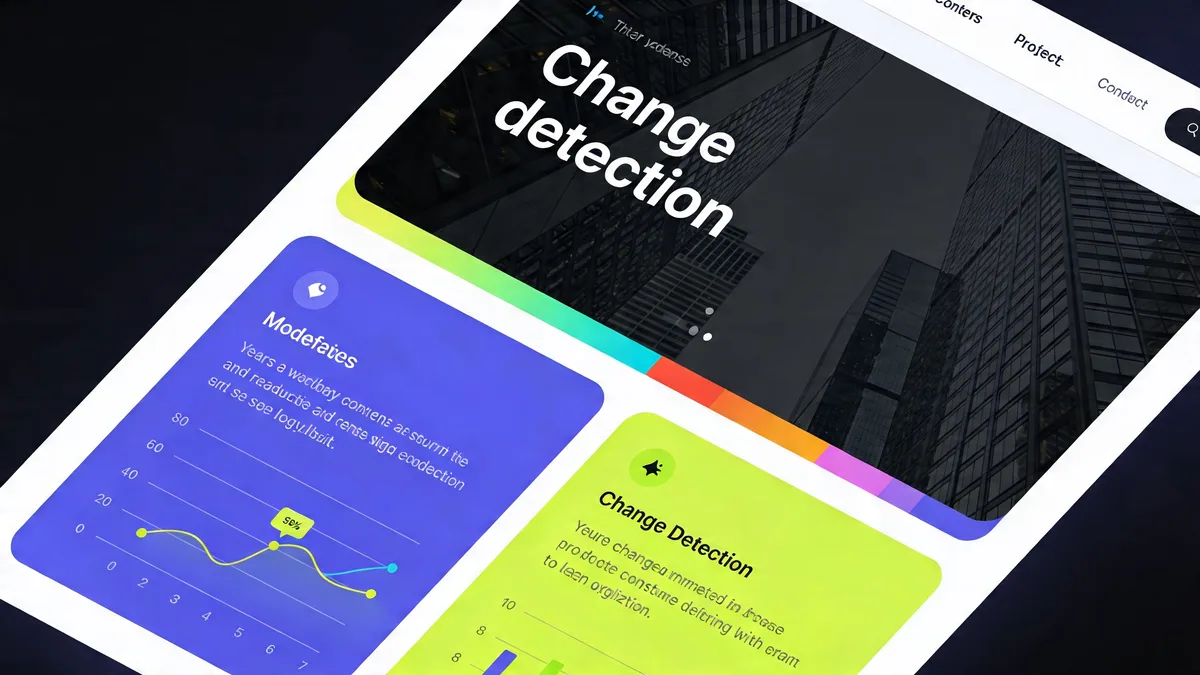
Advanced Detection Strategies for 2026
AI-Powered Anomaly Detection
Agentic AI systems in 2026 can autonomously detect pricing anomalies by learning normal business patterns and flagging deviations that human operators might miss. These systems analyze historical pricing data, seasonal trends, and competitive positioning to identify suspicious changes.
Machine learning models can detect subtle manipulation patterns, such as gradual price increases designed to avoid threshold-based alerts or coordinated changes across related products that suggest systematic tampering.
I've implemented AI-driven detection systems that reduced false positive rates by 75% while catching sophisticated attacks that rule-based systems missed. The key is training models on your specific business patterns rather than relying on generic anomaly detection.
Multi-Layer Monitoring Approach
The most effective content change detection strategies employ six-layer monitoring that includes content changes alongside traditional uptime, performance, SSL, DNS, and visual regression monitoring.
This comprehensive approach catches attacks that might bypass individual monitoring systems. For example, an attacker might modify pricing through DNS hijacking or SSL certificate manipulation, which single-layer content monitoring would miss.
Layer coordination prevents alert storms during legitimate infrastructure changes. When DNS updates occur, content monitoring can temporarily adjust thresholds to account for expected propagation delays.
LLM-Ready Data Governance
Prepare your content structure for AI marketplace compliance by implementing standardized product attributes, consistent naming conventions, and structured data governance policies.
AI agents increasingly penalize sites with inconsistent or poorly structured product information. Content change detection should verify that modifications maintain required schema.org markup and structured data integrity.
Implement governance rules that prevent unauthorized changes to AI-critical elements like product categories, attribute standardization, and pricing format consistency. These elements directly impact visibility in AI-powered search engines and marketplaces.
Responding to Detected Content Changes
Immediate Response Protocols
When content changes are detected, implement a rapid response protocol that prioritizes revenue protection. The first 15 minutes are critical for minimizing financial impact.
Immediate Response Checklist:
- Verify the change - Confirm the alert isn't a false positive
- Assess impact - Determine affected products and potential revenue exposure
- Implement rollback - Restore previous content if unauthorized
- Isolate the source - Identify and secure the compromised system
- Document everything - Maintain detailed incident logs for analysis
I've seen teams reduce average response time from 45 minutes to under 10 minutes by implementing automated verification and rollback procedures for common attack patterns.
Forensic Analysis and Attribution
Once immediate threats are contained, conduct thorough forensic analysis to understand attack vectors and prevent recurrence. Examine access logs, database modification records, and authentication events around the time of detected changes.
Look for patterns that suggest coordinated attacks or insider threats. Multiple simultaneous changes across unrelated products often indicate automated attacks, while targeted modifications might suggest competitor intelligence gathering.
Correlate content changes with infrastructure events, user access patterns, and third-party integration activity. This analysis often reveals security gaps in content management workflows or API access controls.
Prevention and Hardening
Implement principle of least privilege for content management access. Users should only have modification rights for their specific product categories or content areas.
Enable audit trails for all content modifications, including user attribution, change timestamps, and before/after values. This creates accountability and provides forensic evidence for security investigations.
Regular security assessments of content management systems should include penetration testing of admin interfaces, API endpoints, and third-party integrations that can modify product data.
Consider implementing content approval workflows for high-risk changes like pricing modifications or promotional content updates, especially during peak sales periods.
Measuring Success: Key Metrics and KPIs
Time to Detection and Response
Mean Time to Detect (MTTD) unauthorized content changes should be measured in minutes, not hours. Industry benchmarks for critical e-commerce content suggest targeting under 5 minutes for pricing changes and under 15 minutes for other revenue-impacting modifications.
Mean Time to Respond (MTTR) includes the full cycle from detection through containment and resolution. Best-in-class e-commerce operations achieve MTTR under 20 minutes for pricing issues.
Track detection accuracy by measuring false positive and false negative rates. High false positive rates indicate overly sensitive monitoring rules, while false negatives suggest gaps in coverage that attackers could exploit.
Revenue Impact Metrics
Calculate revenue protected through rapid content change detection and response. This metric demonstrates the business value of monitoring investments and helps justify expanded detection capabilities.
Monitor revenue at risk by tracking the potential impact of detected changes if they had gone unaddressed. This helps prioritize monitoring improvements and response procedure optimization.
Measure customer impact through metrics like support ticket volume related to pricing confusion, refund requests due to content inconsistencies, and customer retention rates following content integrity incidents.
Data Integrity Scores
Develop a content integrity score that measures the percentage of critical elements maintaining expected values over time. This provides a high-level health metric for content security.
Track unauthorized change prevention rate by comparing detected incidents to estimated total attack attempts based on access log analysis and security event correlation.
Monitor compliance metrics related to AI marketplace requirements, structured data consistency, and regulatory standards that depend on accurate product information.
Regular assessment of these metrics helps identify trends, validate monitoring effectiveness, and guide security investment decisions. I've found that teams with comprehensive metrics programs detect and respond to content threats 60% faster than those relying on ad-hoc monitoring.
Website content change detection has evolved from a nice-to-have feature to an essential component of e-commerce security and revenue protection. As AI-driven shopping becomes the norm and attack sophistication increases, the teams that implement comprehensive monitoring strategies will maintain their competitive advantage.
The investment in robust content change detection pays dividends through protected revenue, maintained customer trust, and competitive intelligence security. Start with your most critical elements, implement layered monitoring approaches, and continuously refine your detection and response capabilities.
In my experience, the question isn't whether you'll face unauthorized content changes – it's whether you'll detect and respond to them before they impact your bottom line.
Frequently Asked Questions
How quickly can website content change detection identify unauthorized price changes?
Modern content change detection systems can identify unauthorized price modifications within seconds to minutes. Real-time monitoring solutions continuously scan critical elements and trigger immediate alerts when changes occur outside normal business processes.
What types of content changes should e-commerce sites monitor beyond pricing?
E-commerce sites should monitor product descriptions, availability status, promotional banners, shipping information, and payment options. Any content that affects customer decisions or revenue should be included in your monitoring strategy.
Can content change detection prevent competitor price scraping?
While content change detection cannot directly prevent scraping, it can identify unusual access patterns and unauthorized data harvesting attempts. Combined with rate limiting and access controls, it helps protect your pricing intelligence from competitors.
How does AI impact e-commerce content monitoring requirements in 2026?
AI agents now infer product information from dynamic content, making data integrity critical for marketplace visibility. Clean, structured data with consistent pricing attributes is essential to avoid ranking penalties in AI-powered search engines and marketplaces.
What's the difference between visual and text-based content change detection?
Text-based detection monitors raw HTML and data changes, while visual detection captures how changes appear to users. Both are important: text monitoring catches backend tampering, while visual monitoring identifies display issues that could confuse customers.
How should teams respond when unauthorized content changes are detected?
Implement immediate change reversal procedures, conduct forensic analysis to identify the attack vector, and strengthen access controls. Document the incident and update monitoring rules to prevent similar attacks in the future.
Related: Website Content Change Detection (2026) — monitor your site for unauthorized changes with automated tools.
Start Monitoring Your Website for Free
Get 6-layer monitoring, uptime, performance, SSL, DNS, visual, and content checks, with instant alerts when something goes wrong.
Get Started